‘Reset the Net’
ex-iskon-pleme :: Lifestyle :: IT
Page 1 of 2
Page 1 of 2 • 1, 2 
 ‘Reset the Net’
‘Reset the Net’
A coalition of nearly two-dozen tech companies and civil liberties groups is launching a new fight against mass internet surveillance, hoping to battle the NSA in much the same way online campaigners pushed back on bad piracy legislation in 2012.
The new coalition, organized by Fight for the Future, is planning a Reset the Net day of action on June 5, the anniversary of the date the first Edward Snowden story broke detailing the government’s PRISM program, based on documents leaked by the former NSA contractor.
“Government spies have a weakness: they can hack anybody, but they can’t hack everybody,” the organizers behind the Reset the Net movement say in their video (above). “Folks like the NSA depend on collecting insecure data from tapped fiber. They depend on our mistakes, mistakes we can fix.”
To that end, the groups are calling on developers to add at least one NSA resistant feature to mobile apps, and on websites to add security features like SSL (Secure Socket Layer), HSTS (HTTP Strict Transport Security), and Perfect Forward Secrecy to better secure the communication of users and thwart government man-in-the-middle attacks.
They also want mobile apps and websites to post a Reset the Net splash screen on June 5 and are distributing a privacy packet for users that contains a bundle of various free software tools, like Adium and Pidgin (for encrypted chat), Textsecure, and Redphone (encrypted phone calls and text messaging) and GPG (for encrypted email).
Members of the coalition so far include Reddit, Imgur, DuckDuckGo, the Free Software Foundation, and CREDO Mobile, along with a number of civil liberties groups. CREDO Mobile is believed to be the anonymous telecom behind a constitutional battle over the government’s use of National Security Letters to obtain data from telecoms and other companies.
“A year after Snowden’s shocking revelations, the NSA is still spying on innocent Americans without a warrant,” Michael Kieschnick, CEO of CREDO Mobile, said in a statement about the Reset the Net campaign. “CREDO will continue to demand Congress and the president take action to stop unconstitutional mass warrantless surveillance, and until we win real reform, we will encourage users to adopt encryption tools to protect their personal communications from government abuse of the 1st and 4th amendment.”
The call to action recalls a similar grassroots movement that swept the internet in 2012 to protest two federal bills — the Senate’s Protect IP Act and the House’s Stop Online Piracy Act, or SOPA. In that case, thousands of websites went dark or partially dark to halt the legislation. That successful campaign, however, was backed by powerhouse tech firms like Google and Twitter.
So far, none of these companies has joined the coalition.
“We are speaking to different people at a lot of these larger platforms,” says Tiffiniy Cheng, co director of Fight for the Future, which launched the Reset the Net movement. “We’re not sure where we are in those conversation but the conversations are going well.” She notes that the fight against mass surveillance is much more complex than the anti-SOPA campaign, and large companies may take different approaches this time around.
“A lot of companies have either made some public statement or have taken on security practices that would move us towards making mass surveillance very difficult to conduct, so they’re headed in the right direction,” she says. “We expect that they will come out and support the greater movement to make mass surveillance extremely hard to do…. Because the surveillance is done in so many different ways … there are different ways that you can push back on mass surveillance.”
http://www.wired.com/2014/05/reset-the-net/
_________________
"Universal truth is not measured in mass appeal"

shaby- Posts : 284
2014-04-19
 Re: ‘Reset the Net’
Re: ‘Reset the Net’
https://www.resetthenet.org/
https://pack.resetthenet.org/
https://pack.resetthenet.org/
_________________
"Universal truth is not measured in mass appeal"

shaby- Posts : 284
2014-04-19
 Re: ‘Reset the Net’
Re: ‘Reset the Net’
Secret Service Software Will 'Detect Sarcasm' in Social Media Users
The Secret Service is purchasing software to watch users of social networks in real time, according to contract documents
In a work order posted on Monday, the agency details information the tool will collect -- ranging from emotions of Internet users to old Twitter messages.
Its capabilities will include “sentiment analysis,” "influencer identification," "access to historical Twitter data," “ability to detect sarcasm," and "heat maps" or graphics showing user trends by color intensity, agency officials said.
The automated technology will "synthesize large sets of social media data" and "identify statistical pattern analysis" among other objectives, officials said.
The tool also will have the "functionality to send notifications to users,” they said.
A couple of years ago, the Homeland Security Department, the agency's parent, got in trouble with lawmakers and civil liberties groups for a social media program that would work, in part, by having employees create fake usernames and profiles to spy on other users.
A House Homeland Security Committee panel called DHS officials into a hearing after reports the department tasked analysts with collecting data that reflected negatively on the government, such as content about the transfer of Guantanamo detainees to a Michigan jail. The Electronic Privacy Information Center has sued DHS for more information on the program.
Employees within the Secret Service's Office of Government and Public Affairs will be using the new system, agency officials said.
Here is a full list of the software’s required functions:
http://www.nextgov.com/defense/2014/06/secret-service-software-will-detect-sarcasm-social-media-users/85633/
The Secret Service is purchasing software to watch users of social networks in real time, according to contract documents
In a work order posted on Monday, the agency details information the tool will collect -- ranging from emotions of Internet users to old Twitter messages.
Its capabilities will include “sentiment analysis,” "influencer identification," "access to historical Twitter data," “ability to detect sarcasm," and "heat maps" or graphics showing user trends by color intensity, agency officials said.
The automated technology will "synthesize large sets of social media data" and "identify statistical pattern analysis" among other objectives, officials said.
The tool also will have the "functionality to send notifications to users,” they said.
A couple of years ago, the Homeland Security Department, the agency's parent, got in trouble with lawmakers and civil liberties groups for a social media program that would work, in part, by having employees create fake usernames and profiles to spy on other users.
A House Homeland Security Committee panel called DHS officials into a hearing after reports the department tasked analysts with collecting data that reflected negatively on the government, such as content about the transfer of Guantanamo detainees to a Michigan jail. The Electronic Privacy Information Center has sued DHS for more information on the program.
Employees within the Secret Service's Office of Government and Public Affairs will be using the new system, agency officials said.
Here is a full list of the software’s required functions:
- Real-time stream analysis;
- Customizable, keyword search features;
- Sentiment analysis;
- Trend analysis;
- Audience segmentation;
- Geographic segmentation;
- Qualitative, data visualization representations (heat maps, charts, graphs, etc.);
- Multiple user access;
- Functionality to have read-only users;
- Access to historical twitter data;
- Influencer identification;
- Standard web browser access with login credentials;
- User level permissions;
- Compatibility with Internet Explorer 8;
- Section 508 compliant;
- Ability to detect sarcasm and false positives;
- Functionality to send notifications to users;
- Functionality to analyze data over a given period of time;
- Ability to quantify the agency's social media outreach/footprint;
- Vendor-provided training and technical/customer support;
- Ability to create custom reports without involving IT specialists; and
- Ability to search online content in multiple languages.
http://www.nextgov.com/defense/2014/06/secret-service-software-will-detect-sarcasm-social-media-users/85633/
_________________
"Universal truth is not measured in mass appeal"

shaby- Posts : 284
2014-04-19
 Re: ‘Reset the Net’
Re: ‘Reset the Net’
Hvala shaby.Puno korisnih linkova. I na mojim stranicama sutra će se pojaviti
Reset the Net splash screen
Reset the Net splash screen

Trinity-

Posts : 12923
2014-04-17
 Re: ‘Reset the Net’
Re: ‘Reset the Net’
nikog više ne podrzavam.eno na,podrzao kreatora Fajerfoxa,jer je bio grub prema gejama,pa ga iz korporacije izbacili,i od tga trena stalno traze podrsku...sada fiancijsku.. e mauna.. 


Guest- Guest
 Re: ‘Reset the Net’
Re: ‘Reset the Net’
ma ima i ovdje gumb "donate", samo malo je teže od mene izvući money... 


Trinity-

Posts : 12923
2014-04-17
 Re: ‘Reset the Net’
Re: ‘Reset the Net’
ne radi tako...
to je skup besplatnih alata kojima štitiš svoje mailove, chatove, lozinke, onemogućuju praćenje i tvoje navike kod surfanja...
to je skup besplatnih alata kojima štitiš svoje mailove, chatove, lozinke, onemogućuju praćenje i tvoje navike kod surfanja...

Trinity-

Posts : 12923
2014-04-17
 Re: ‘Reset the Net’
Re: ‘Reset the Net’
Spotfux ...vrlo sam zadovoljan..no nekomercijalna verzija,pa malo usporava,ali sto radi sa data streamom,to je čudo..

Guest- Guest
 Re: ‘Reset the Net’
Re: ‘Reset the Net’
What is Tor ?
Tor: Overview
Inception
Tor was originally designed, implemented, and deployed as a third-generation onion routing project of the U.S. Naval Research Laboratory. It was originally developed with the U.S. Navy in mind, for the primary purpose of protecting government communications. Today, it is used every day for a wide variety of purposes by normal people, the military, journalists, law enforcement officers, activists, and many others.
Overview
Tor is a network of virtual tunnels that allows people and groups to improve their privacy and security on the Internet. It also enables software developers to create new communication tools with built-in privacy features. Tor provides the foundation for a range of applications that allow organizations and individuals to share information over public networks without compromising their privacy.
Individuals use Tor to keep websites from tracking them and their family members, or to connect to news sites, instant messaging services, or the like when these are blocked by their local Internet providers. Tor's hidden services let users publish web sites and other services without needing to reveal the location of the site. Individuals also use Tor for socially sensitive communication: chat rooms and web forums for rape and abuse survivors, or people with illnesses.
Journalists use Tor to communicate more safely with whistleblowers and dissidents. Non-governmental organizations (NGOs) use Tor to allow their workers to connect to their home website while they're in a foreign country, without notifying everybody nearby that they're working with that organization.
Groups such as Indymedia recommend Tor for safeguarding their members' online privacy and security. Activist groups like the Electronic Frontier Foundation (EFF) recommend Tor as a mechanism for maintaining civil liberties online. Corporations use Tor as a safe way to conduct competitive analysis, and to protect sensitive procurement patterns from eavesdroppers. They also use it to replace traditional VPNs, which reveal the exact amount and timing of communication. Which locations have employees working late? Which locations have employees consulting job-hunting websites? Which research divisions are communicating with the company's patent lawyers?
A branch of the U.S. Navy uses Tor for open source intelligence gathering, and one of its teams used Tor while deployed in the Middle East recently. Law enforcement uses Tor for visiting or surveilling web sites without leaving government IP addresses in their web logs, and for security during sting operations.
The variety of people who use Tor is actually part of what makes it so secure. Tor hides you among the other users on the network, so the more populous and diverse the user base for Tor is, the more your anonymity will be protected.
Why we need Tor
Using Tor protects you against a common form of Internet surveillance known as "traffic analysis." Traffic analysis can be used to infer who is talking to whom over a public network. Knowing the source and destination of your Internet traffic allows others to track your behavior and interests. This can impact your checkbook if, for example, an e-commerce site uses price discrimination based on your country or institution of origin. It can even threaten your job and physical safety by revealing who and where you are. For example, if you're travelling abroad and you connect to your employer's computers to check or send mail, you can inadvertently reveal your national origin and professional affiliation to anyone observing the network, even if the connection is encrypted.
How does traffic analysis work? Internet data packets have two parts: a data payload and a header used for routing. The data payload is whatever is being sent, whether that's an email message, a web page, or an audio file. Even if you encrypt the data payload of your communications, traffic analysis still reveals a great deal about what you're doing and, possibly, what you're saying. That's because it focuses on the header, which discloses source, destination, size, timing, and so on.
A basic problem for the privacy minded is that the recipient of your communications can see that you sent it by looking at headers. So can authorized intermediaries like Internet service providers, and sometimes unauthorized intermediaries as well. A very simple form of traffic analysis might involve sitting somewhere between sender and recipient on the network, looking at headers.
But there are also more powerful kinds of traffic analysis. Some attackers spy on multiple parts of the Internet and use sophisticated statistical techniques to track the communications patterns of many different organizations and individuals. Encryption does not help against these attackers, since it only hides the content of Internet traffic, not the headers.
The solution: a distributed, anonymous network

Tor helps to reduce the risks of both simple and sophisticated traffic analysis by distributing your transactions over several places on the Internet, so no single point can link you to your destination. The idea is similar to using a twisty, hard-to-follow route in order to throw off somebody who is tailing you — and then periodically erasing your footprints. Instead of taking a direct route from source to destination, data packets on the Tor network take a random pathway through several relays that cover your tracks so no observer at any single point can tell where the data came from or where it's going.
To create a private network pathway with Tor, the user's software or client incrementally builds a circuit of encrypted connections through relays on the network. The circuit is extended one hop at a time, and each relay along the way knows only which relay gave it data and which relay it is giving data to. No individual relay ever knows the complete path that a data packet has taken. The client negotiates a separate set of encryption keys for each hop along the circuit to ensure that each hop can't trace these connections as they pass through.

Once a circuit has been established, many kinds of data can be exchanged and several different sorts of software applications can be deployed over the Tor network. Because each relay sees no more than one hop in the circuit, neither an eavesdropper nor a compromised relay can use traffic analysis to link the connection's source and destination. Tor only works for TCP streams and can be used by any application with SOCKS support.
For efficiency, the Tor software uses the same circuit for connections that happen within the same ten minutes or so. Later requests are given a new circuit, to keep people from linking your earlier actions to the new ones.

Hidden services
Tor also makes it possible for users to hide their locations while offering various kinds of services, such as web publishing or an instant messaging server. Using Tor "rendezvous points," other Tor users can connect to these hidden services, each without knowing the other's network identity. This hidden service functionality could allow Tor users to set up a website where people publish material without worrying about censorship. Nobody would be able to determine who was offering the site, and nobody who offered the site would know who was posting to it. Learn more about configuring hidden services and how the hidden service protocol works.
Staying anonymous
Tor can't solve all anonymity problems. It focuses only on protecting the transport of data. You need to use protocol-specific support software if you don't want the sites you visit to see your identifying information. For example, you can use the Tor Browser Bundle while browsing the web to withhold some information about your computer's configuration.
Also, to protect your anonymity, be smart. Don't provide your name or other revealing information in web forms. Be aware that, like all anonymizing networks that are fast enough for web browsing, Tor does not provide protection against end-to-end timing attacks: If your attacker can watch the traffic coming out of your computer, and also the traffic arriving at your chosen destination, he can use statistical analysis to discover that they are part of the same circuit.
The future of Tor
Providing a usable anonymizing network on the Internet today is an ongoing challenge. We want software that meets users' needs. We also want to keep the network up and running in a way that handles as many users as possible. Security and usability don't have to be at odds: As Tor's usability increases, it will attract more users, which will increase the possible sources and destinations of each communication, thus increasing security for everyone. We're making progress, but we need your help. Please consider running a relay or volunteering as a developer.
Ongoing trends in law, policy, and technology threaten anonymity as never before, undermining our ability to speak and read freely online. These trends also undermine national security and critical infrastructure by making communication among individuals, organizations, corporations, and governments more vulnerable to analysis. Each new user and relay provides additional diversity, enhancing Tor's ability to put control over your security and privacy back into your hands.
https://www.torproject.org
Tor: Overview
Inception
Tor was originally designed, implemented, and deployed as a third-generation onion routing project of the U.S. Naval Research Laboratory. It was originally developed with the U.S. Navy in mind, for the primary purpose of protecting government communications. Today, it is used every day for a wide variety of purposes by normal people, the military, journalists, law enforcement officers, activists, and many others.
Overview
Tor is a network of virtual tunnels that allows people and groups to improve their privacy and security on the Internet. It also enables software developers to create new communication tools with built-in privacy features. Tor provides the foundation for a range of applications that allow organizations and individuals to share information over public networks without compromising their privacy.
Individuals use Tor to keep websites from tracking them and their family members, or to connect to news sites, instant messaging services, or the like when these are blocked by their local Internet providers. Tor's hidden services let users publish web sites and other services without needing to reveal the location of the site. Individuals also use Tor for socially sensitive communication: chat rooms and web forums for rape and abuse survivors, or people with illnesses.
Journalists use Tor to communicate more safely with whistleblowers and dissidents. Non-governmental organizations (NGOs) use Tor to allow their workers to connect to their home website while they're in a foreign country, without notifying everybody nearby that they're working with that organization.
Groups such as Indymedia recommend Tor for safeguarding their members' online privacy and security. Activist groups like the Electronic Frontier Foundation (EFF) recommend Tor as a mechanism for maintaining civil liberties online. Corporations use Tor as a safe way to conduct competitive analysis, and to protect sensitive procurement patterns from eavesdroppers. They also use it to replace traditional VPNs, which reveal the exact amount and timing of communication. Which locations have employees working late? Which locations have employees consulting job-hunting websites? Which research divisions are communicating with the company's patent lawyers?
A branch of the U.S. Navy uses Tor for open source intelligence gathering, and one of its teams used Tor while deployed in the Middle East recently. Law enforcement uses Tor for visiting or surveilling web sites without leaving government IP addresses in their web logs, and for security during sting operations.
The variety of people who use Tor is actually part of what makes it so secure. Tor hides you among the other users on the network, so the more populous and diverse the user base for Tor is, the more your anonymity will be protected.
Why we need Tor
Using Tor protects you against a common form of Internet surveillance known as "traffic analysis." Traffic analysis can be used to infer who is talking to whom over a public network. Knowing the source and destination of your Internet traffic allows others to track your behavior and interests. This can impact your checkbook if, for example, an e-commerce site uses price discrimination based on your country or institution of origin. It can even threaten your job and physical safety by revealing who and where you are. For example, if you're travelling abroad and you connect to your employer's computers to check or send mail, you can inadvertently reveal your national origin and professional affiliation to anyone observing the network, even if the connection is encrypted.
How does traffic analysis work? Internet data packets have two parts: a data payload and a header used for routing. The data payload is whatever is being sent, whether that's an email message, a web page, or an audio file. Even if you encrypt the data payload of your communications, traffic analysis still reveals a great deal about what you're doing and, possibly, what you're saying. That's because it focuses on the header, which discloses source, destination, size, timing, and so on.
A basic problem for the privacy minded is that the recipient of your communications can see that you sent it by looking at headers. So can authorized intermediaries like Internet service providers, and sometimes unauthorized intermediaries as well. A very simple form of traffic analysis might involve sitting somewhere between sender and recipient on the network, looking at headers.
But there are also more powerful kinds of traffic analysis. Some attackers spy on multiple parts of the Internet and use sophisticated statistical techniques to track the communications patterns of many different organizations and individuals. Encryption does not help against these attackers, since it only hides the content of Internet traffic, not the headers.
The solution: a distributed, anonymous network

Tor helps to reduce the risks of both simple and sophisticated traffic analysis by distributing your transactions over several places on the Internet, so no single point can link you to your destination. The idea is similar to using a twisty, hard-to-follow route in order to throw off somebody who is tailing you — and then periodically erasing your footprints. Instead of taking a direct route from source to destination, data packets on the Tor network take a random pathway through several relays that cover your tracks so no observer at any single point can tell where the data came from or where it's going.
To create a private network pathway with Tor, the user's software or client incrementally builds a circuit of encrypted connections through relays on the network. The circuit is extended one hop at a time, and each relay along the way knows only which relay gave it data and which relay it is giving data to. No individual relay ever knows the complete path that a data packet has taken. The client negotiates a separate set of encryption keys for each hop along the circuit to ensure that each hop can't trace these connections as they pass through.

Once a circuit has been established, many kinds of data can be exchanged and several different sorts of software applications can be deployed over the Tor network. Because each relay sees no more than one hop in the circuit, neither an eavesdropper nor a compromised relay can use traffic analysis to link the connection's source and destination. Tor only works for TCP streams and can be used by any application with SOCKS support.
For efficiency, the Tor software uses the same circuit for connections that happen within the same ten minutes or so. Later requests are given a new circuit, to keep people from linking your earlier actions to the new ones.

Hidden services
Tor also makes it possible for users to hide their locations while offering various kinds of services, such as web publishing or an instant messaging server. Using Tor "rendezvous points," other Tor users can connect to these hidden services, each without knowing the other's network identity. This hidden service functionality could allow Tor users to set up a website where people publish material without worrying about censorship. Nobody would be able to determine who was offering the site, and nobody who offered the site would know who was posting to it. Learn more about configuring hidden services and how the hidden service protocol works.
Staying anonymous
Tor can't solve all anonymity problems. It focuses only on protecting the transport of data. You need to use protocol-specific support software if you don't want the sites you visit to see your identifying information. For example, you can use the Tor Browser Bundle while browsing the web to withhold some information about your computer's configuration.
Also, to protect your anonymity, be smart. Don't provide your name or other revealing information in web forms. Be aware that, like all anonymizing networks that are fast enough for web browsing, Tor does not provide protection against end-to-end timing attacks: If your attacker can watch the traffic coming out of your computer, and also the traffic arriving at your chosen destination, he can use statistical analysis to discover that they are part of the same circuit.
The future of Tor
Providing a usable anonymizing network on the Internet today is an ongoing challenge. We want software that meets users' needs. We also want to keep the network up and running in a way that handles as many users as possible. Security and usability don't have to be at odds: As Tor's usability increases, it will attract more users, which will increase the possible sources and destinations of each communication, thus increasing security for everyone. We're making progress, but we need your help. Please consider running a relay or volunteering as a developer.
Ongoing trends in law, policy, and technology threaten anonymity as never before, undermining our ability to speak and read freely online. These trends also undermine national security and critical infrastructure by making communication among individuals, organizations, corporations, and governments more vulnerable to analysis. Each new user and relay provides additional diversity, enhancing Tor's ability to put control over your security and privacy back into your hands.
https://www.torproject.org

Trinity-

Posts : 12923
2014-04-17
 Re: ‘Reset the Net’
Re: ‘Reset the Net’
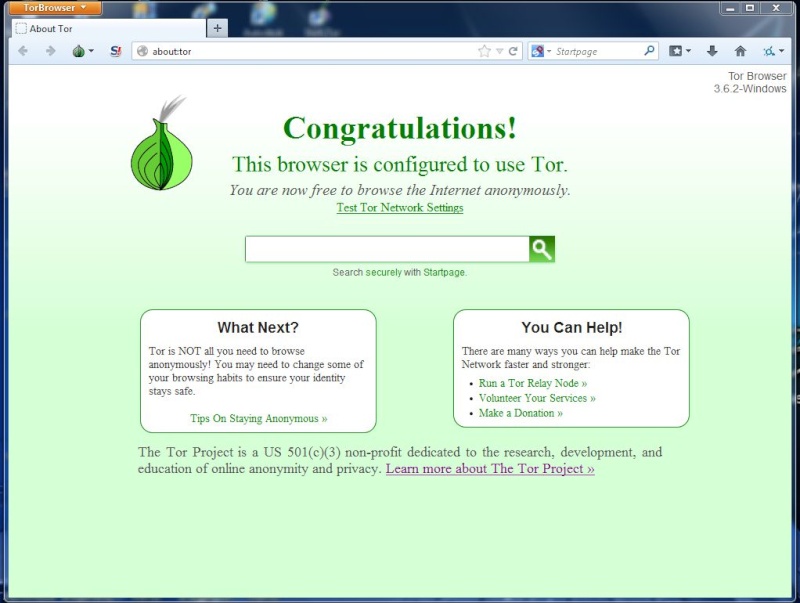
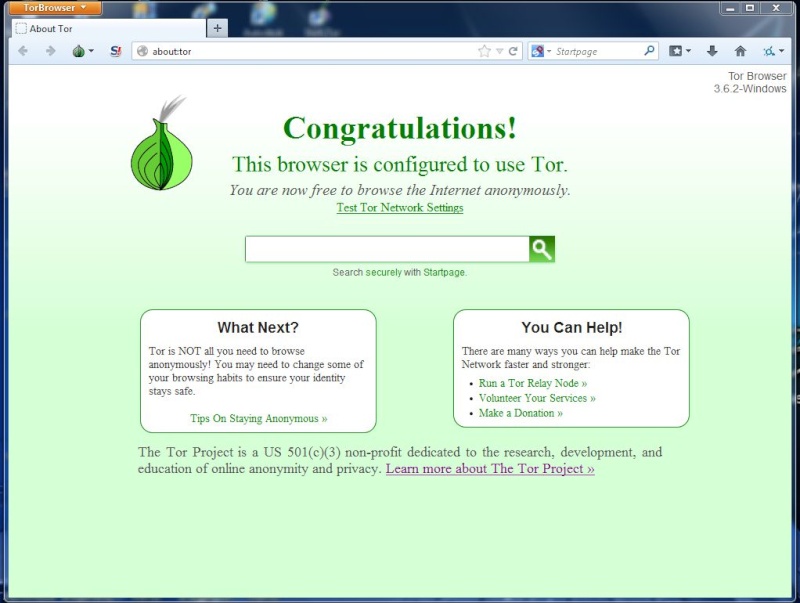
Ovako izgleda Tor aplikacija (browser) nakon pokretanja...

Trinity-

Posts : 12923
2014-04-17
 Re: ‘Reset the Net’
Re: ‘Reset the Net’
lukić...usporaa sarfanje do bola...sad,mozda je komercijalna verzija nes brza

Guest- Guest
 Re: ‘Reset the Net’
Re: ‘Reset the Net’
je....malo usporava, ali s obzirom na način rada nije ni čudo...
koliko vidim nema komercijalne verzije...
ti koristiš Spotfux, jel šta brži?
koliko vidim nema komercijalne verzije...
ti koristiš Spotfux, jel šta brži?

Trinity-

Posts : 12923
2014-04-17
 Re: ‘Reset the Net’
Re: ‘Reset the Net’
uhhh,spotflux je opak..no podosta usporaa jer radi opako kriptiranje u oblaku,i ostalo..procitaj na houmpejdžu,inače je jako siguran...moj prvi izbor,cak i prije Hotspot shielda

Guest- Guest
 Re: ‘Reset the Net’
Re: ‘Reset the Net’
Tor preporučuju ovi sa bitcoin.org i ovi sa resettheneta, pogledat ću malo i taj spotfux

Trinity-

Posts : 12923
2014-04-17
Page 1 of 2 • 1, 2 
 Similar topics
Similar topics» The Great Reset (episode 1)
» Great reset & klimatske promijene
» Reset Daytona: Zahtjev Srpske koji će podržati i Hrvati
» world economic forum- great reset of capitalism will only work if it includes everyone
» Davos Great Reset: French Prez Macron Declares Modern Capitalism ‘Can No Longer Work’
» Great reset & klimatske promijene
» Reset Daytona: Zahtjev Srpske koji će podržati i Hrvati
» world economic forum- great reset of capitalism will only work if it includes everyone
» Davos Great Reset: French Prez Macron Declares Modern Capitalism ‘Can No Longer Work’
ex-iskon-pleme :: Lifestyle :: IT
Page 1 of 2
Permissions in this forum:
You cannot reply to topics in this forum
 Events
Events Latest images
Latest images
 by shaby 4/6/2014, 21:28
by shaby 4/6/2014, 21:28




 THX... samo jedan dobar VPN i sve rješeno..
THX... samo jedan dobar VPN i sve rješeno.. 